Cybersecurity in 2026 is no longer driven by novelty or fear-based narratives. Most organizations already operate in cloud-native, distributed environments where security tooling is abundant and threats are constant. The challenge IT teams face today is not a lack of solutions, but a lack of clarity. With expanding attack surfaces and growing operational complexity, teams are searching for approaches that actually reduce risk without slowing delivery.
What IT teams look for in 2026 reflects a shift in priorities. Security is no longer treated as a separate function layered on top of systems. It is increasingly evaluated as part of platform design, operational resilience, and day-to-day engineering work. Trends that matter are those that help teams operate more predictably under pressure — not those that promise absolute protection.
- In 2026, IT teams prioritize security approaches that integrate into architecture and workflows rather than introduce friction.
- What matters most is reducing complexity, limiting blast radius, and enabling faster response.
- What loses relevance are tool-heavy strategies, manual controls, and security models disconnected from how systems are actually built and operated.
Security as an Operating Reality, Not a Special Case
One of the defining cybersecurity trends in 2026 is the normalization of threat presence. IT teams no longer operate under the assumption that systems are either secure or compromised. Instead, they design environments where compromise is possible but contained.
This mindset reshapes security priorities. Rather than focusing exclusively on prevention, teams search for ways to ensure that failures remain localized, access can be revoked quickly, and systems recover without cascading disruption. Security becomes an operating condition, not an exception.
Reducing Complexity as a Security Strategy
As digital infrastructures scale, complexity itself becomes a primary risk factor. Overlapping tools, inconsistent policies, and fragmented ownership introduce blind spots that attackers exploit more effectively than sophisticated technical vulnerabilities. In many modern environments, failures emerge not from unknown exploits, but from systems that are too complex to reason about under pressure.
The impact of complexity is measurable. Industry analyses consistently show that the majority of cloud and security incidents — often estimated at 60–70% — stem from misconfiguration, excessive permissions, or unclear system boundaries, rather than from novel attack techniques. Each additional platform, integration, or exception increases the number of possible failure paths and reduces overall visibility.

In response, IT teams in 2026 actively seek simplification. Fewer platforms with clearly defined responsibilities outperform layered security stacks that no single team fully understands. When ownership is explicit and systems are standardized, security issues become easier to detect, diagnose, and contain. Standardized environments reduce variance, making abnormal behavior stand out rather than blend into noise.
Identity, Access, and Ownership Take Center Stage
While perimeter-based security continues to fade, identity-driven security remains central. IT teams search for ways to make access explicit, temporary, and auditable. Broad permissions and long-lived credentials are recognized as structural liabilities.
Just as important is ownership. Security incidents escalate most often where responsibility is unclear. In 2026, teams prioritize models where ownership of services, data, and access is visible and enforced. This clarity allows faster decisions during incidents and reduces reliance on centralized intervention.
Security Integrated Into Platforms and Pipelines
Another clear trend in 2026 is the shift from security as a process to security as a platform capability. Manual reviews, approval workflows, and external security checkpoints do not scale in environments built around continuous delivery. As deployment frequency increases, these controls become bottlenecks rather than safeguards. IT teams increasingly look for security that is enforced by default through infrastructure, configuration, and deployment pipelines.
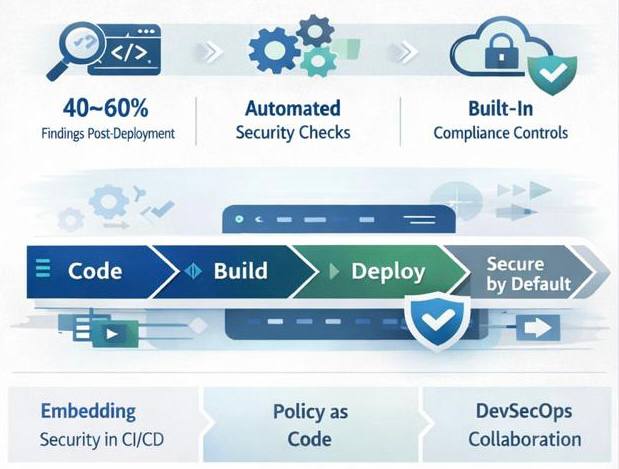
The limitations of manual security controls are well documented. In fast-moving cloud environments, manual reviews often occur too late, after risky configurations are already deployed. Organizations report that a significant portion of security findings — commonly 40–60% — emerge after changes reach shared or production environments, when remediation is more expensive and disruptive. This reactive model creates friction without reliably reducing risk.
Observability Over Alerts
Alert fatigue remains a persistent issue in 2026. IT teams are less interested in more alerts and more focused on meaningful signals. The trend moves toward observability that helps teams understand system behavior and detect anomalies early, rather than react to every deviation.
Security insights that integrate with operational visibility are valued more than isolated security dashboards. Teams want to see how security events relate to system performance, access patterns, and user behavior in context.
What Loses Relevance in 2026
Several long-standing security practices continue to lose traction. Annual audits without continuous validation provide little protection in fast-changing environments. Documentation-heavy compliance efforts fail under real-world pressure. Tool adoption without ownership and integration increases noise without improving outcomes.
IT teams increasingly reject security strategies that slow delivery without measurably reducing risk.
Conclusion
Cybersecurity trends in 2026 reflect a maturing perspective within IT teams. The focus shifts from chasing threats to designing systems that remain stable, observable, and controllable under attack. What teams search for are not silver bullets, but approaches that align security with architecture, ownership, and daily operations.
Security becomes effective when it is predictable, embedded, and aligned with how systems are built and run. In a landscape of constant threat, the strongest advantage is not perfect defense, but controlled impact and fast recovery.
Looking for a team to design or scale secure cloud platforms for modern IT environments?
Contact us!Why Ficus Technologies?
Ficus Technologies operates at the intersection of cloud platforms, security-aware architecture, and scalable digital systems. This positioning reflects the reality of modern cloud environments, where security, governance, analytics, and delivery can no longer be treated as separate concerns.
As cloud platforms grow in scale and complexity, many organizations struggle not with the lack of tools, but with fragmentation between architecture, operations, and control models. Security is added after the fact, governance relies on manual processes, and analytics evolves independently from platform design. These disconnects increase risk, cost volatility, and operational friction over time.
Trends that reduce complexity, improve ownership, and integrate security directly into platforms and workflows.
Not entirely, but their value depends on how well they integrate into system design and daily operations.
Clarity, predictability, and the ability to respond quickly when incidents occur.
No. It is equally an architectural and organizational challenge shaped by ownership and operating models.