Layer 2 networks have become core infrastructure for production blockchain systems. By 2026, scalable execution environments are no longer optional for products with growing transaction volume or user bases. The pressure is not only financial, driven by gas costs, but architectural. Users expect predictable fees and fast confirmation, while teams require sustainable scaling without weakening security guarantees.
For products already operating on Layer 1, integrating Layer 2 is not a reset. It is an extension of an existing system with live liquidity, governance processes, and operational dependencies. The question is not whether to deploy on Layer 2, but how to integrate it without introducing fragmentation or systemic risk.
It is particularly relevant for DeFi protocols, tokenized asset platforms, NFT ecosystems, and high-throughput consumer applications seeking scalability while maintaining trust and composability.
- Layer 2 integration reshapes architectural boundaries and trust assumptions.
- Bridging design often defines the dominant security risk.
- Liquidity, governance, and monitoring must evolve together with execution logic.
- Scalability succeeds only when cross-layer coordination is explicit.
What Layer 2 Means in 2026
Layer 2 networks are scaling solutions that process transactions outside the main blockchain while still inheriting the security guarantees of the underlying Layer 1.
Most modern Layer 2 systems use rollup architectures, where transactions are executed off-chain but posted back to Ethereum for validation. Two dominant categories exist:
1. Optimistic rollups, which assume transactions are valid unless challenged.
2. Zero-knowledge rollups, which verify state changes using cryptographic proofs.
From a product perspective, Layer 2 networks function almost like independent chains. They have their own RPC endpoints, block explorers, token bridges, and infrastructure providers. However, they remain cryptographically anchored to Ethereum.
For developers integrating Layer 2 into an existing product, this creates a hybrid environment: applications must support multiple execution layers while maintaining a consistent user experience.
The future of blockchain scalability will be built on layers.
Gavin Wood, Co-founder of Ethereum & Polkadot
Architectural Integration Models
Existing products typically adopt one of three structural patterns when integrating Layer 2.
The extension model keeps core contracts and settlement logic on Layer 1 while moving high-frequency interactions to Layer 2. This preserves composability and base-layer security guarantees but introduces cross-layer message synchronization complexity. Oracle feeds, collateral logic, and governance updates must remain consistent across environments.
The mirrored deployment model recreates contract logic on both Layer 1 and Layer 2, allowing users to choose where to transact. While this lowers friction and distributes load, it fragments liquidity and requires disciplined upgrade coordination. Without canonical token definitions and unified governance execution, mirrored systems drift.
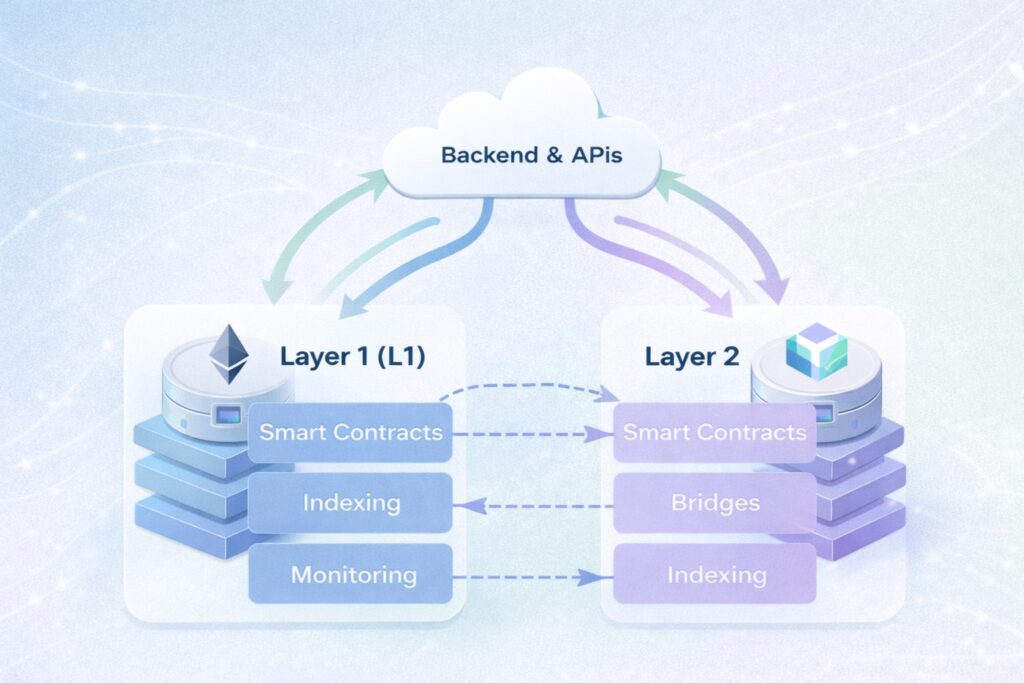
The migration-with-settlement model shifts primary execution to Layer 2 while using Layer 1 as a security anchor and dispute layer. This maximizes throughput and user affordability but increases dependence on bridge reliability and sequencer integrity. The operational risk surface changes accordingly.
The correct model depends on transaction patterns, liquidity structure, and governance architecture rather than fee optimization alone.
Bridging Assets and Data
One of the most complex parts of Layer 2 integration is bridging — the mechanism that moves tokens or data between Layer 1 and Layer 2 networks.
Most rollups rely on canonical bridges that lock assets on Ethereum while minting equivalent tokens on the Layer 2 network. However, the bridging process introduces several challenges.
First, bridging is asynchronous. Transactions moving from L1 to L2 can take minutes, while withdrawals from L2 back to L1 may require challenge periods depending on the rollup design.

Second, user experience must account for these delays. Applications need clear UI feedback during bridging operations and reliable transaction tracking.
Third, liquidity management becomes essential. Many teams integrate third-party bridges or liquidity providers to reduce withdrawal delays and improve UX.
Designing bridging flows carefully is critical, as they represent one of the most common failure points in cross-chain products.
Liquidity, State, and Governance Coordination
Layer 2 expansion changes where liquidity resides and how state transitions are validated.
Fragmented liquidity reduces depth and increases arbitrage volatility. Centralized liquidity increases dependence on bridging infrastructure. Token canonicalization, reward distribution, and treasury management must reflect cross-layer flows.
Governance architecture must also extend coherently. Teams must define whether governance executes on Layer 1, Layer 2, or across both through synchronized mechanisms. Parameter updates and emergency controls should not diverge between environments.
Without clear coordination, systems appear functional under normal conditions but expose inconsistencies during market stress or network congestion.
Operational and Monitoring Implications
Layer 2 integration increases the number of operational dependencies. Sequencer uptime, data availability assumptions, and bridge health monitoring must become part of production observability.
Monitoring tools must aggregate Layer 1 and Layer 2 events coherently. Incident response procedures should account for cross-layer failure scenarios. Finality expectations differ between layers and must be reflected in liquidation logic, settlement timing, and reporting.
Operational readiness determines whether scalability improves resilience or introduces blind spots.
Deployment Considerations in 2026
The Layer 2 ecosystem in 2026 includes multiple dominant rollups and modular data availability layers. Each network carries distinct decentralization timelines, tooling ecosystems, and liquidity gravity.
Selecting a Layer 2 is therefore an ecosystem alignment decision. Integration must account for long-term roadmap compatibility, developer tooling maturity, and liquidity access.
Scalability decisions that ignore ecosystem dynamics often create future migration pressure.
Let’s build scalable blockchain products together!
Contact usConclusion
Layer 2 networks have fundamentally reshaped the blockchain scalability landscape. In 2026, they are no longer optional enhancements but essential infrastructure for decentralized applications aiming to reach mass adoption.
For existing products, integrating Layer 2 requires thoughtful architecture changes, secure bridging mechanisms, and reliable deployment strategies. When executed correctly, the payoff is significant: faster transactions, dramatically lower fees, and a smoother user experience.
The companies that succeed will not simply deploy to Layer 2 — they will design their systems to operate across layers, creating resilient and scalable blockchain architectures.
Why Ficus Technologies?
Integrating Layer 2 into an existing product is not just a technical upgrade — it is a strategic architectural shift. Teams must rethink smart contract design, infrastructure layers, bridging mechanisms, and deployment pipelines while maintaining the stability of a live product.
At Ficus Technologies, we help companies navigate this transition with confidence. Our engineers combine deep expertise in blockchain architecture, smart contract development, and scalable infrastructure, ensuring that Layer 2 integrations are secure, efficient, and production-ready.
We support clients through the entire process — from evaluating the right Layer 2 ecosystem and designing multi-layer architectures to implementing bridging strategies and deployment pipelines. Our approach focuses on performance, security, and long-term maintainability, allowing products to scale without compromising reliability.
The primary risk lies in bridging and cross-layer message validation rather than in core contract logic.
Layer 2 can preserve base-layer security when designed correctly, but it shifts trust assumptions toward bridge and sequencer mechanisms.
No. Liquidity coordination and canonical token design can mitigate fragmentation, but they must be explicitly structured.
When transaction volume, user cost sensitivity, and scalability constraints outweigh the added architectural and operational complexity.